7:00 – 4:00 ASRC MKT
- Make more obvious the Inadvertent Social Information and Digital ISI
- ISI
- Trails
- Visual clustering
- Behavior around the commons (waterholes)
- Presence of young
- Mating behavior
- etc.
- DISI
- Words and their overall source (Social media, website content, contributor content, auto-generated, etc)
- Votes (likes, kudos, karma points)
- Money (site income, blockchain ledger)
- Linking (href, retweet, share)
- Images & videos
- ISI
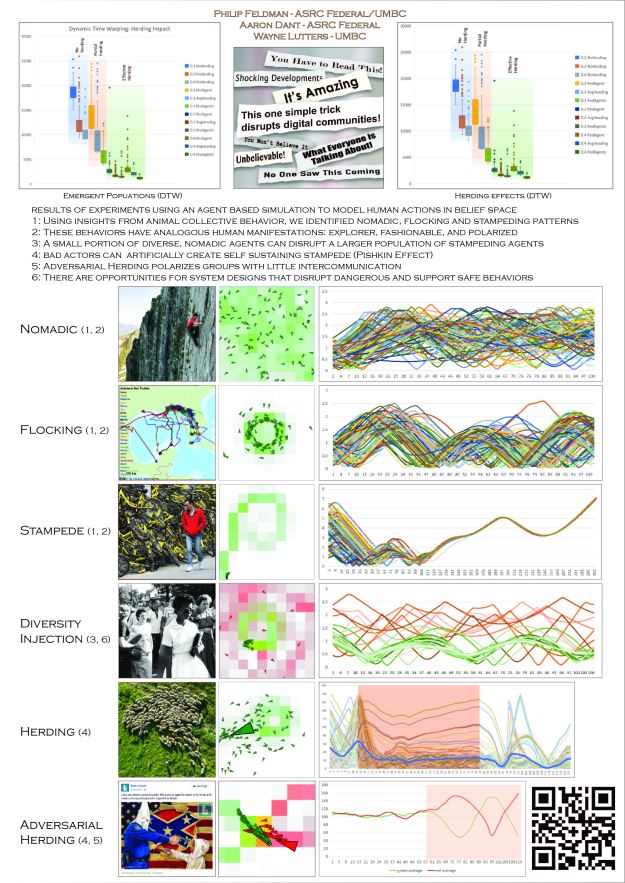
- Work more on behavior patterns of humans and animals
- Highly organized (soccer match singing, marching, mass dancing events)
- Wildebeest feeding, defending,migrating and stampeding
- AutoKeras is a GitHub project that uses the ENAS algorithm. It can be installed using pip. Since it’s written in Keras it’s quite easy to control and play with, so you can even dive into the ENAS algorithm and try making some modifications. If you prefer TensorFlow or Pytorch, there’s also public code projects for those here and here!
- From Zeynep’s twitter
- So, Russian trolls amplified divisive content and helped spread vaccine misinformation. Look, the challenge before us is to redefine *critical thinking* to include figuring out what to believe, not just how to be skeptical. Personal and institutional.
- Weaponized Health Communication: Twitter Bots and Russian Trolls Amplify the Vaccine Debate
- Whereas bots that spread malware and unsolicited content disseminated antivaccine messages, Russian trolls promoted discord. Accounts masquerading as legitimate users create false equivalency, eroding public consensus on vaccination.
- Trying to decode podcasts. Here’s my test, and here are the results from Google speech-to-text:
- We were talking about the choices of who’s you can keep two of these three, I guess Adonis Alexander is along for the ride, huh? I thought I was about to I didn’t know I haven’t I haven’t sent it to him. Well, has he been out there? They might missing some guys got to hand. I kept thinking like if to say, they weren’t having these injuries. Like if they have like us to say, okay, but they have these reason iron Marshall and maybe he maybe he’s not available week one, but they don’t want to put them on IR prn’s things up. So maybe they have to add another running back like you so you have to create a roster spot I could imagine this is just speculation Alexander. Somehow gets the mysterious injury to put them on I are clearly my keys ready, right and they they would have five cornerbacks otherwise and you know, yeah, if you’re not going to be ready to go, but you may have to you know, go get okay. Yeah. I mean the he’s he’s a guy that I think is on based on these the way the wrong.
- It’s pretty good as long as people aren’t stepping over each other verbally.
- Good enough to try, I guess. Noisy data is life, right? Look for the bigger signal.
- Here’s my current plan. It’s a half-assed first approach, but it should provide some insight.
- Download a season of a sports podcast and put each podcast into it’s own document Here’s the tutorial for Speech-to-text with REST
- Use Corpus Manager to convert, using BOW and create an ignore list for common words like “the”
- then read all the docs into LMN
- Then set the weight of each successive document (in time) so that its top
- Take the top ten words and save them to a file
- Try building a map







You must be logged in to post a comment.