7:15 – 6:00 ASRC MKT
- More Bit by Bit
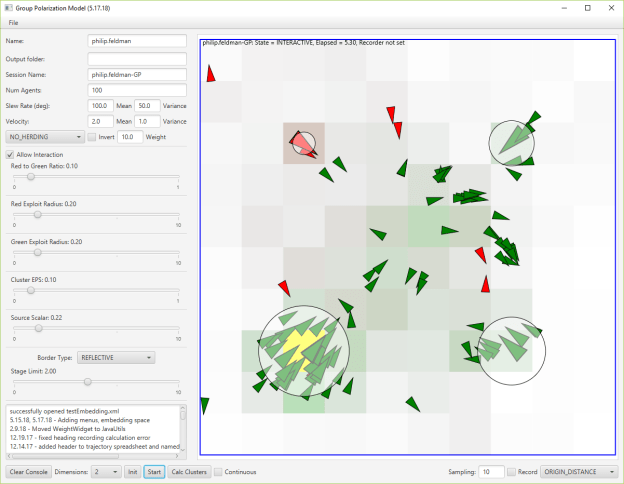
- An interesting tweet about the dichotomy between individual and herd behaviors.
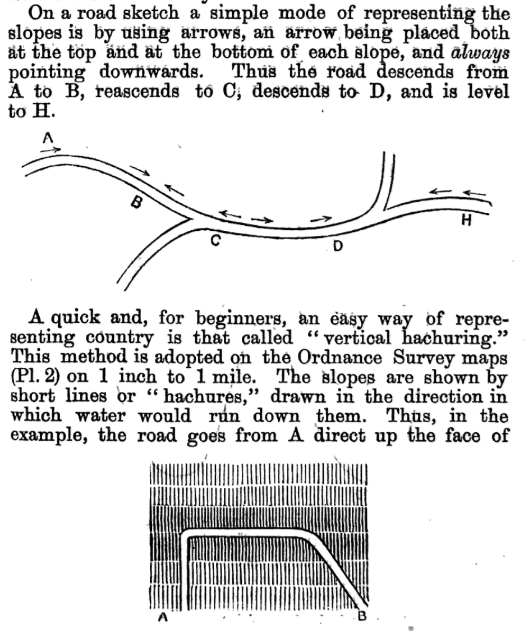
- More white paper. Add something about awareness horizon, and how maps change that from a personal to a shared reality (cite understanding ignorance?)
- Great discussion with Aaron about incorporating adversarial herding. I think that there will be three areas
- Thunderdome – affords adversarial herding. Users have to state their intent before joining a discussion group. Bots and sock puppets allowed
- Clubhouse – affords discussion with chosen individuals. THis is what I thought JuryRoom was
- JuryRoom – fully randomized members and topics, based on activity in the Clubhouse and Thunderdome






You must be logged in to post a comment.