7:00 – 2:00 ASRC PhD/BD
- Today’s big though: Maps are going top be easier than I thought. We’ve been doing them for thousands of years with board games.
- Worked with Aaron on slides, including finding fault detection using our technologies. There is quite a bit, with pioneering work from NASA
- Uploaded documents – done
- Called and left messages for Dr. Wilkins and Dr. Palazzolo. Need to send a follow-up email to Dr. Palazzolo and start on the short white papers
- Leaving early to vote
- The following two papers seem to be addressing edge stiffness
- Model of the Information Shock Waves in Social Network Based on the Special Continuum Neural Network
- The article proposes a special class of continuum neural network with varying activation thresholds and a specific neuronal interaction mechanism as a model of message distribution in social networks. Activation function for every neuron is fired as a decision of the specific systems of differential equations which describe the information distribution in the chain of the network graph. This class of models allows to take into account the specific mechanisms for transmitting messages, where individuals who, receiving a message, initially form their attitude towards it, and then decide on the further transmission of this message, provided that the corresponding potential of the interaction of two individuals exceeds a certain threshold level. The authors developed the original algorithm for calculating the time moments of message distribution in the corresponding chain, which comes to the solution of a series of Cauchy problems for systems of ordinary nonlinear differential equations.
- A cost-effective algorithm for inferring the trust between two individuals in social networks
- The popularity of social networks has significantly promoted online individual interaction in the society. In online individual interaction, trust plays a critical role. It is very important to infer the trust among individuals, especially for those who have not had direct contact previously in social networks. In this paper, a restricted traversal method is defined to identify the strong trust paths from the truster and the trustee. Then, these paths are aggregated to predict the trust rate between them. During the traversal on a social network, interest topics and topology features are comprehensively considered, where weighted interest topics are used to measure the semantic similarity between users. In addition, trust propagation ability of users is calculated to indicate micro topology information of the social network. In order to find the top–k most trusted neighbors, two combination strategies for the above two factors are proposed in this paper. During trust inference, the traversal depth is constrained according to the heuristic rule based on the “small world” theory. Three versions of the trust rate inference algorithm are presented. The first algorithm merges interest topics and topology features into a hybrid measure for trusted neighbor selection. The other two algorithms consider these two factors in two different orders. For the purpose of performance analysis, experiments are conducted on a public and widely-used data set. The results show that our algorithms outperform the state-of-the-art algorithms in effectiveness. In the meantime, the efficiency of our algorithms is better than or comparable to those algorithms.
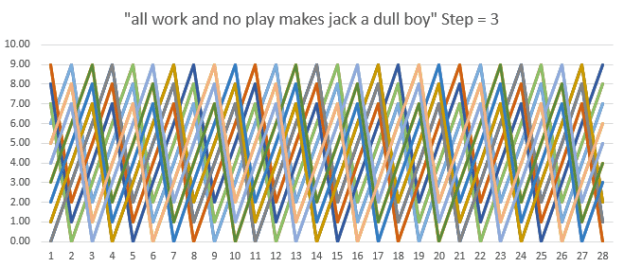
- Back to LSTMs. Made a numeric version of “all work and no play in the jack_torrance generator
- Reading in and writing out weight files. The predictions seems to be working well, but I have no insight into the arguments that go into the LSTM model. Going to revisit the Deep Learning with Keras book
